Corporate cyber security, as an industry, is about to hit the big payload. Corporate IT teams around the world are already in overdrive, pushed by a near-panicked CEO, calling around to figure out the right systems and solutions. Consultancies who have positioned themselves in this space are going to have a bonanza helping companies to configure these new systems. It’s a function of human nature that it takes a rude wake-up call to see the writing on the wall. On the one hand, the risk of leaked information has been with us since the printed word – it’s just that the scale and scope of the leaks has expanded. On the other hand, the trend toward greater transparency has been evident for years, ever since the Internet surfaced. The types of information and the intentions of the hack/theft vary tremendously. Even unveiling an ugly corporate culture (prevalent, backstabbing, rampant nepotism or management by fear, etc) could be considered “sensitive” information.
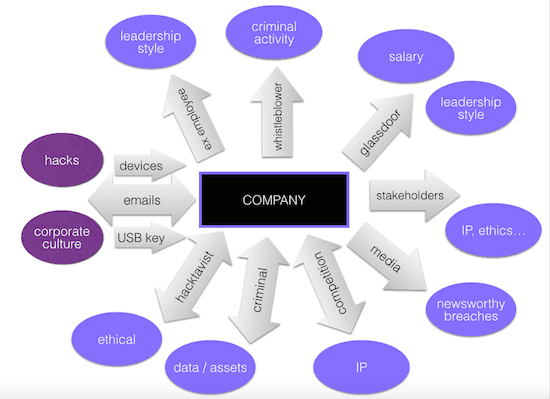
In the figure above, the grey arrows indicate the conduits for the leaks and the purple bubbles identify the nature of the theft/leak.
The opportunities for information of a sensitive nature to escape from within have been mushrooming with every new device and channel of communication. The digital nature of communications has made the access and amplification potential of a security breach geometrically more risky. {Tweet this!} The digitalization of data, following Moore’s Law, has been getting ever more efficient, but it has also made it much more portable.
In the past year, we have seen examples of major breaches of virtually every type:
- Hacktavists – Anonymous Brazil went after the World Cup 2014
- Criminal – SONY, for the most obvious one, but we can add all the incursions at Target, JP Morgan, Home Depot and, most recently, Staples…
- Media – Apple’s factory conditions reported via a hidden camera in the BBC Panorama report
- Whistleblowers – Just ask Bank of America
- Disgruntled Employee – Morrisons in the UK
- Glassdoor – the worst rated companies to work for (in the US) and the worst-rated CEOs or as reported here by WallSt
Check out this great infographic, provided by Information is Beautiful, that shows a history of the big breaches over the years, starting in 2004.
 Corporate cyber insecurity
Corporate cyber insecurity
In short, the walls of security around a company are becoming increasingly porous. One approach in terms of corporate cyber security — that will surely be favored by a lot of running-scared CEOs — will be to shore up the defenses and try to block all the holes. This will prove fatally insufficient and worringly closed-minded. Having been to Samsung’s Digital City just outside Seoul, Korea (pictured right), where anyone entering their huge facilities needs to have an inspection and security clearance of a caliber one might expect at the Fairfax Virginia FBI facilities, you can feel how being so “closed off” can have an impact on the ambiance within. It is one drastic way to try to address the problem; but even that is surely not enough to fend off a serious threat of leakage.
Balancing act
The delicate balancing act facing senior leadership is to secure the truly strategic material while not closing the company off from the outside. And the trick is to do this all the while enabling a transparency that fosters trust and a more genuine and engaged community within and without the company. Perhaps, the pink elephant in the closet is when the senior leaders are part of the problem. If IT has its hands full with these cyber security challenges, I wager that HR (along with the entire Executive Committee) should be equally, if not more concerned and mobilized, because at its heart, the issue of cyber security is also, endemically, one of corporate culture. Moreover, on the talent front, data security specialists and those with a “safe” hacker mentality will increasingly be available only at a major premium.
Your thoughts and reactions welcome!
***If you like my writing and are interested in fostering more meaningful conversations in our society, please check out my Dialogos Substack. This newsletter will feature articles on why and how we can all improve our conversations, whether it’s at home, with friends, in society at large or at work. Subscription is free, but if you see value in it, you are welcome to contribute both materially and through your comments. Sign up here:










Trackbacks/Pingbacks